Demystifying the Shared Responsibility Model in SaaS Security: Who Handles What?

Navigating the world of Software as a Service (SaaS) offers incredible benefits, but it also introduces complexities, especially concerning security. A fundamental concept you absolutely must grasp is the Shared Responsibility Model in SaaS security. Misunderstanding this framework can lead to dangerous security gaps, data breaches, and compliance failures. This post breaks down exactly what the shared responsibility model entails for SaaS applications and what you, as the customer, need to manage.
Understanding the Shared Responsibility Model in SaaS is the first step towards robust cloud security. Essentially, it’s a framework outlining which security tasks are handled by the SaaS vendor and which fall under your purview as the customer. It’s not about shifting blame, but clarifying duties to ensure comprehensive protection.
What is the Shared Responsibility Model?
Think of it like renting a secure apartment. The landlord (SaaS provider) is responsible for the security *of* the building – the main doors, the structural integrity, the fire alarms. However, you, the tenant (SaaS customer), are responsible for securing what’s *inside* your apartment – locking your door, not giving keys to strangers, and securing your valuables.
In the SaaS context, the provider manages the security of the underlying infrastructure that runs the service (servers, networks, physical security) and often the core application software itself. The customer, conversely, is responsible for how they *use* the service, primarily focusing on data security, user access, and client-side security.
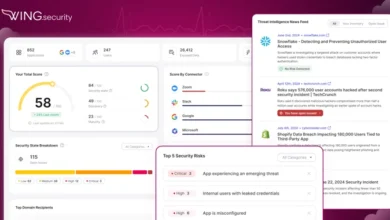
[Hint: Insert image/video of A diagram visually splitting responsibilities between SaaS Provider (Infrastructure, App Operation) and Customer (Data, Access, Configuration) here]
SaaS Provider Responsibilities: Security *OF* the Cloud
While specifics can vary slightly between providers (always check your Service Level Agreement – SLA!), the SaaS vendor generally takes ownership of:
- Infrastructure Security: Protecting the physical data centers, servers, networking equipment, and virtualization layers that host the SaaS application.
- Application Security (Core): Ensuring the SaaS application code itself is developed securely, patched against vulnerabilities, and functions correctly.
- Operational Security: Managing the day-to-day operations, uptime, disaster recovery, and basic monitoring of the service platform.
- Compliance (Platform Level): Often adhering to broad compliance standards like SOC 2 or ISO 27001 for their infrastructure and operations.
Their goal is to provide a secure and reliable platform on which customers can operate.
Customer Responsibilities: Security *IN* the Cloud
This is where many organizations stumble. Just because you’re using a SaaS application doesn’t mean you can abdicate all security tasks. Customers typically retain critical responsibilities, including:
Data Security and Classification
You own your data. This means you are responsible for:
- Identifying and Classifying Sensitive Data: Knowing what data you’re putting into the SaaS application (PII, financial data, intellectual property) and classifying its sensitivity.
- Data Loss Prevention (DLP): Implementing controls, often within the SaaS application’s settings or via third-party tools, to prevent sensitive data from leaving inappropriately.
- Encryption (Where Applicable): Configuring available encryption options for data at rest or in transit, beyond the provider’s baseline.
Identity and Access Management (IAM)
Controlling who can access the SaaS application and what they can do is paramount:
- User Provisioning/Deprovisioning: Adding new users, assigning appropriate permissions (principle of least privilege), and promptly removing access when users leave or change roles.
- Authentication: Enforcing strong passwords, enabling multi-factor authentication (MFA) – a critical defense layer.
- Access Reviews: Regularly reviewing user permissions to ensure they are still appropriate.
Configuration and Settings Management
SaaS applications often provide numerous security settings that customers must configure correctly:
- Security Settings: Enabling features like audit logging, session timeouts, IP restrictions, and specific security modules offered by the vendor.
- Integration Security: Ensuring secure configuration if integrating the SaaS app with other systems.
Client-Side Security
Protecting the devices and networks used to access the SaaS application:
- Endpoint Security: Ensuring user devices (laptops, mobiles) have antivirus, are patched, and are secure.
- Network Security: Protecting the local network from which users access the SaaS service.
Why Understanding the Model is Critical
Ignoring your part of the Shared Responsibility Model in SaaS can have severe consequences. Breaches often occur not because the SaaS provider failed, but because the customer misconfigured settings, granted excessive permissions, or didn’t monitor user activity. According to recent cloud security reports, misconfiguration remains a leading cause of cloud data breaches. Understanding your duties helps ensure regulatory compliance (like GDPR or CCPA), protects sensitive data, and maintains business continuity.
For more detailed perspectives from major providers, you can review frameworks like the AWS Shared Responsibility Model, which outlines principles common across cloud services.
Taking Control of Your SaaS Security
Don’t assume the vendor handles everything. Proactively manage your responsibilities:
- Read the Fine Print: Carefully review your SaaS vendor’s SLA and documentation regarding their security measures and your responsibilities.
- Configure Wisely: Dedicate time to understand and configure all available security settings within the SaaS application.
- Master Access Control: Implement robust IAM practices, enforce MFA, and conduct regular access reviews.
- Monitor Activity: Utilize available logs and monitoring tools to watch for suspicious activity related to your data and user accounts.
- Educate Users: Train employees on secure practices for using SaaS applications, password hygiene, and phishing awareness.
By actively participating in the Shared Responsibility Model in SaaS, you significantly enhance your security posture and leverage the full potential of SaaS without compromising safety. For further insights on related topics, explore our guide on choosing secure SaaS vendors.